|
The debate about whether Android phones are better than the iPhone has been a long debate, with neither side budging ... until now. And it looks like the advantage Apple has is at a fundamental basic level. Read here to get the scoop!
#iphoneipad #android #reviews
0 Comments
Google Maps has a feature that shows how long you can expect to wait at places like restaurants and stores. By knowing how busy a place is, and how long of a wait you can expect, you can save time by planning to go on another day or at a different time. Check it out here!
#google #iphoneipad #android #techhacks There are a lot of navigation apps in the iOS and Android stores, but the three major players are: Waze, Google Maps, and Apple Maps. Each has its advantages and disadvantages. Find out here which is best for you!
#reviews #google #iphoneipad #android That's right! All someone needs is a one-minute sampling of your voice to clone it! Using artifical intelligence, this company can clone your "voice DNA" to not only generate sentences with your voice, but with human emotions like anger, stress or sympathy. So powerful, it can generate 1,000 real-time sentences in less than a half a second. Of course, there are ethical concerns despite the practical uses such as virtual assistants, audio book reading with celebrity voices, speech synthesis for the disabled and for voice-overs for movies and video games. Get the scoop here.
#news #security If you don’t have the need or the budget to upgrade your smartphone, then the next best thing is buying an upgrade for the phone you’ve already got. Cases, battery packs, and wireless charging pads are the obvious calls, but there are a ton of more exciting upgrades out there! Check them out here!
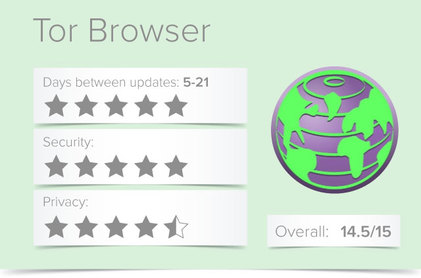
#iphoneipad #android #techgadgets Developed by The Tor Project in 2002, and based on Firefox’s browser, the Tor Browser was built for users to access the internet anonymously via the Tor network. Your activity and identity are masked by Tor, which encrypts your traffic in at least three layers by “bouncing your communications around a distributed network of relays” selected from thousands of volunteer computers.
Tor (originally called The Onion Router because it layers your traffic like an onion) is a free network of servers, or ‘nodes’, that randomly route internet traffic between each other in order to obfuscate the origin of the data. The Tor Browser can significantly increase a user’s privacy and anonymity online. In internal documents, the NSA even refers to Tor as “the king of high-secure, low latency internet anonymity.” Tor does not replace your VPN, as it only anonymizes your browsing and a few other select services (which need to be specifically configured). Connecting to Tor through VPN connection is a great way to maintain your internet privacy and security. Not only will it hide your browsing data from your VPN company, it will also hide your home IP address from the Tor entry node. Find out more about the Tor Browser here. As always, The GoTo Tech Guru is here to help with your security issues & concerns! #security Sometimes a file is just too large to email either due to excessive upload/download time or ISP limits. When this happens, the alternative is to send a link to the file. But you don't want that link sitting out there forever nor for people to have unlimited download ability. You also want security. Introducing Mozilla Send. This cross-browser web app allows you to send self-destructing files (via a link) up to 1GB for free! The link will only work for 24 hours or for a certain number of downloads, whichever comes first. But that's not all it offers! Check it out here!
#security Every time you run a search online, the websites where you maintain an account can record that information. This data—collected and stored by search engines like Google, social media networks like Facebook, and retail giants like Amazon — won't disappear when you erase your browser's search history. Here's how to purge your search history on some of the biggest and most popular search engines, social media networks, and retail websites.
#security #google Logging in with Facebook, the social network's universal login API, allows users to carry their profile information to other apps and websites. You've probably used it to log in to services like Spotify, Airbnb, and Tinder. But sometimes, especially on lesser known websites, using Facebook's universal login feature may carry security risks. Find out what to do here!
#security |
Blog AuthorI love technology and how it enhances our lives! Just think, without the Apollo moon missions, we might not have calculators! Imagine!! Archives
October 2018
Categories
All
|






 RSS Feed
RSS Feed