|
Whether you are being censored by your government or a private or public organization, you know that online censorship is more common than people think. Connecting to a VPN is easy to do and will solve the problem most of the time. However, you may have experienced some situations that stop that process. Those include blockades by governments, schools, colleges, and even many private companies. If you are not in the targeted area to view some content, you will be blocked because of geo-restrictions.
This guide will help you bypass VPN restrictions. As always, The GoTo Tech Guru is here to help with any questions or the implementation of VPN on your computers. #security
0 Comments
A Virtual Private Network (VPN) redirects your connection to the Internet via a remote server run by a VPN provider. This way, the VPN server becomes a secure launching pad for you before you access various websites. All the network traffic between your device and the VPN server is directed through a secure virtual tunnel. All of the data sent and received is encrypted. Best of all, your device appears to have the IP address of the VPN server, protecting your true identity. As far as websites are concerned, you’re browsing from the server’s geographical location, not your computer’s location.
There are two types of VPN, which are different and can make a difference depending on your goal. This article will explain the differences and how best to leverage them. As always, The GoTo Tech Guru is here to help with any questions or the implementation of VPN on your computers. #security Your smartphone is a remarkable feat of engineering. It’s half a dozen or more gadgets packed into a single slab. Much of it’s coolest feats are accomplished with a wide range of sensors — but what are they and what do they all actually do?
Here’s all you need to know. #iphoneipad #android How does it work and is it really all that superior to just plugging your phone into the wall every night? Here’s what you need to know about wireless charging, including the Pros and Cons, and what you need to make it work.
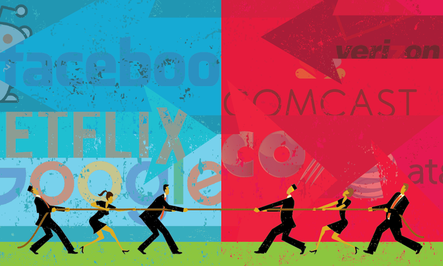
#iphoneipad #android #techgadgets Original Net Neutrality regulations, enacted in 2015, classified broadband service as a Title II utility under the Communications Act. Basically, ISPs could not discriminate against any legal content. Nor could ISPs slow down access to websites or services based on their content if they were lawful
Net neutrality is dead. Additionally, ISPs could not create “fast lanes,” which give consumers or companies who paid an extra fee faster service. The Federal Communications Commission’s (FCC) rollback of net neutrality protections officially kicked in on Monday, June 11, 2018. Find out that this means to you here. #netneutrality The appeal of escaping Google comes down to privacy. Google collects an alarming amount of data about you. To understand how Google does this, how it affects you, and how to delete your data from Google to protect yourself and be off-the-grid, see this article.
#security #google Ever received a file and found out that none of your installed programs can open it? Not every computer has the same programs, program versions or even the same fonts. And what looks fine on your computer might look terrible, or not even open at all, on someone else's system. It may be as simple as converting the unknown file type to something your computer DOES understand! For file conversions of virtually any type, this use free online converter!
#software Check out these 10 handy, fun and downright helpful ways to use USB thumb drives.
#techgadgets #mac #windows #security #software Google provides users with several other security options, some of which you may have never heard of. Find out here!
#google #security These secret features are easy to use. They can help you make your computer run faster, stream media to multiple devices, share content with your family, turn a regular old letter into a professional-looking document and much more. Click here for the load-down!
#windows Here are some everyday Windows 10 tips to help you organize and maximize your productivity to get you back into the (work)-flow of things.
#windows Like most things with technology, it's not a simple yes or no answer. "It all depends on the make and model of the device. If you're able to get into the phone, there's always a chance for you to recover deleted text messages. Getting the texts you want, that's up in the air. If you're looking to recover deleted data, we're at the mercy of what's left on the device." says Trent Leavitt, manager of computer forensics at Decipher Forensics. Read here to find all the in's & out's.
#iphoneipad #android #security |
Blog AuthorI love technology and how it enhances our lives! Just think, without the Apollo moon missions, we might not have calculators! Imagine!! Archives
October 2018
Categories
All
|









 RSS Feed
RSS Feed