|
Cybercrime, data breaches, and internet attacks are on the rise. In fact, it is estimated that the global economy will lose around $2 trillion by 2019 due to cybercrime. Through your router, Hackers can hijack and harvest your personal information, commandeer your smart devices, install malware on your computer and redirect your traffic to fake websites. This newly discovered malware campaign does precisely that. If you're not careful about, cybercriminals can quickly all drain your bank accounts without warning! Enter Roaming Mantis, which propagates itself not via third-party app downloads nor phishing scams but via a technique known as DNS hijacking via your router! Find out here how to protect yourself!
#virus&malware #android #security #wifi
0 Comments
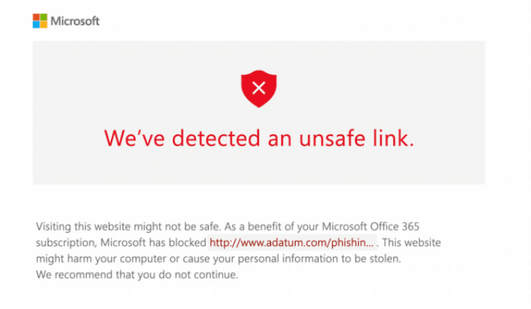
Microsoft is building anti-ransomware functionality into its OneDrive cloud storage solution that can help mitigate the damage. These are features that were first introduced for OneDrive for Business and that the company is now pushing to anyone who’s signed up for an Office 365 Home or Personal subscription. The features work together to help users recover their files in the event of a ransomware attack. Read all about it here!
#security #virus&malware Microsoft has announced that Windows Defender, its built-in antivirus software for Windows 10, will start removing software that has “coercive messages” or “misleading content to pressure you into paying for additional services or performing superfluous actions.”
This type of software, commonly known as scareware, is typically found in cleaner apps that will supposedly optimize your registry on a Windows PC or promise to otherwise speed a machine up. “There has been an increase in free versions of programs that purport to scan computers for various errors, and then use alarming, coercive messages to scare customers into buying a premium version of the same program. See this article to understand more and what to do. #windows #security #news The latest attacks involving cryptocurrencies such as Bitcoin are outsmarting even the biggest tech companies around. Click on the wrong site and your computer could be hijacked by those looking to profit from cryptocurrency. While browsing online, you might suddenly hear your laptop’s fans whirring into life and your PC slowing to a crawl. A security scan might show no malicious files hiding in your PC. The problem goes away, and you move on. And yet, when you next come back to that same website, the problem starts again. The cause could be a type of malware that’s very hard to detect. In fact, when used legitimately, this software isn’t considered malware at all. Find out here what's going on! Learn more here about cryptocurrency, like Bitcoin,
#security #virus&malware Design flaws in processors from leading chipmakers could let attackers access sensitive information. The flaw impacts more than just Windows, Macs and iOS devices and affects most all computers, phones, tablets, watches, smart TVs and the like.
This is a flaw in the computer CPU chips at its most fundamental level and is NOT a virus, so cannot be eradicated by anti-virus or anti-malware software. It will require several levels of fixes to include no less than: the operating system, BIOs, and CPU driver. At this time, no hardware replacements are necessary, just firmware and software fixes. However, due to repair complexity, if not done properly and by a professional, it could render your device completely useless, otherwise known as "bricking". For questions or to have your computer repaired, call The GoTo Tech Guru! How did this happen and what's the fix? #security #news #iphoneipad #chromebook #mac #tv #virus&malware #windows #android A new method of hacking devices via Bluetooth has been recently revealed. The potential threat is to for Android, iOS, Windows and Linux devices as well as many common household gadgets often referred to as IoT (Internet of Things) devices. If you're device Bluetooth radio is turned on, even if the device is locked, BlueBorne can hack it!
Get the specifics here! As always, The GoTo Tech Guru is here to help! #security #wifi #virus&malware #news A new and highly-sophisticated variant of the malicious Panda Zeus malware is capable of exploiting Google’s standard search results to trick unwary consumers into providing their banking credentials over the web, as highlighted in a blog post published by the Cisco-System’s-owned Talos earlier this week.
This malware “poisons” Google’s search engine results using Search Engine Optimization (SEO), essentially so that “fake bank-related results” are shuffled to the top of the first page, according to a FOX News report. Users searching for bank-related information such as branch locations, hours, or to open a new account online are being tricked into clicking a fake and malicious link which ostensibly looks harmless, but ultimately infects their system with the virus. Read here for more information and on how to protect yourself! As always, The GoTo Tech Guru is here to help with this as well as all your I.T. needs! #virus&malware #news This week, the (Chinese) Malware KeyBoy was discovered again, this time specifically targeting Western countries rather than Far East countries previously. It uses legitimate Microsoft Word documents to piggyback malware that can transparently record keystrokes, take screenshots, gather system information, browse and download files, shutdown and reboot victim machines.
This allows the hacker to steal online passwords in real-time literally as you type them, take screenshots while you review your online bank + financial statements and download any file that's on your computer ... all this without you knowing!! What makes this malware even more tricky is that the Microsoft Word file is actually a valid document that you can open and edit! First, after installing itself, it deletes the original piggybacked file so it's more difficult to trigger a malware warning. Then it disables pop-ups so any warnings your virus or malware prevention software may issue is suppressed. Bottomline: This malware is more difficult to catch and people are lulled into a false sense of security since the Microsoft Word file is a real document. Don't be it's next victim! Contact The GoTo Tech Guru so you are properly protected against KeyBoy! Read more on this malware here. #virus&malware #news A new breed of Android ransomware has been discovered that hits victims with a double whammy. DoubleLocker not only encrypts data as all ransomware does, it also changes the PIN on the target device.
DoubleLocker was discovered by security researchers at ESET. They say that the ransomware abuses Android accessibility settings, and is the first to use a double-lock approach. Based on previously released banking malware, it is though that a test version of DoubleLocker could have been in the wild since as early as May. Despite the banking roots, the ransomware is focused purely on extracting money from victims as a ransom -- it is not capable of accessing banking details stored on a phone or tablet. DoubleLocker spreads as a fake version of Adobe Flash Player, and it uses a clever trick to ensure that it gets activated -- enabling accessibility services and then setting itself as the default home app. Once active, DoubleLocker will first change the device's PIN to a random number. It is not stored on the target device, so there is no way to determine what it is. This is the first incentive for a victim to pay a ransom, and once this has been paid, the PIN can be remotely reset. Encrypting data using AES encryption algorithm, appending the extension ".cryeye" is the second incentive. If you have a backup of your data, it is possible to remove the ransomware without having to cough up any money. Otherwise, it will be next to impossible without wiping your phone to factory settings, which will result in loss of everything that is on your phone. But not all is lost as most data these days, such as Gmail and Contacts are actually stored in the cloud and can be easily resync'd with your reset phone. For other possible options on recovering your phone without your Pin, read this blog article: What if You Forget your Android Phone's Password? Learn more here or call The Go To Tech Guru for assistance! #news #android #virus&malware Several security flaws in the Wi-Fi Protected Access 2 (WPA2) protocol were recently disclosed, which can reportedly expose any wireless device. An attacker within range of a victim can exploit these weaknesses using Key Reinstallation Attacks (KRACKs). Attackers can use this attack technique to read information that was previously assumed to be safely encrypted by easily getting your Wi-Fi password. This can be abused to steal sensitive information such as credit card numbers, passwords, chat messages, emails, photos, and so on. The attack works against all modern protected Wi-Fi networks. Depending on the network configuration, it is also possible to inject and manipulate data. For example, an attacker might be able to inject ransomware or other malware into websites or seemingly legitimate files you may download.
The weaknesses are in the Wi-Fi standard itself, and not in individual products or implementations. Therefore, any correct implementation of WPA2 is likely affected. To prevent the attack, users must update affected products as soon as security updates become available. Note that if your device supports Wi-Fi, it is most likely affected. Microsoft has already released a patch for Windows, so be sure to update your computer! Versions include: Windows 7, Windows 8.1, Windows 10, Windows Server 2008, Windows Server 2012 and Windows Server 2016. You can find every patch for KRACK here. Use the following methods to protect yourself: 1. Do NOT use Wi-Fi in public or other dense areas such as office / apartment / condo buildings. 2. Use an Ethernet cable instead of Wi-Fi. 3. Use a Virtual Private Network (VPN). 4. Use your phone data instead of Wi-Fi. 5. Use HTTPS instead of HTTP urls. You can add a HTTPS Everywhere browser extension to Google Chrome, Firefox or Opera. There’s no need to configure it, so anybody can do it. In most cases, this extension will allow HTTP urls to use HTTPS instead. Read here for the gory details. As always, The GoTo Tech Guru is here to help protect you. #security #virus&malware #windows #wifi #news The Newest Ransomware Threat and how your Personal & Client Data could be released to the Public!9/28/2017 As if ransomware wasn’t bad enough, there is a new twist called doxware. The term "doxware" is a combination of doxing — posting hacked personal information online — and ransomware. Attackers notify victims that their sensitive, confidential or personal files will be released online. If contact lists are also stolen, the perpetrators may threaten to release information to the lists or send them links to the online content.
One of the earliest doxware attacks, Ransoc, informed victims that files violating intellectual property rights or files containing child pornography were present on their computers; unless the victim remitted a payment, the authorities would be notified and the victim would be incarcerated. With access to more devices, attackers could refine doxware attacks that make it cost-effective to target individuals on a massive scale. Although ransomware prevention software can be put in place, nothing is a 100% guarantee against being attacked. Protect the data on your PC so that even if stolen by Doxware, it can't be read or used. Read here for more details. Call The Go To Tech Guru for a consultation on how to protect your data! #security #news #virus&malware A combination of common sense, backup, proactive protection, and automated removal tools is a solid defense against the growing scourge of ransomware. Ransomware doesn’t sneak into your PC like ordinary malware. It bursts in, points a gun at your data, and screams for cash—or else. And if you don’t learn to defend yourself, it could happen again and again, as the recent WannaCry outbreak is demonstrating. Read this article on protecting yourself. As always, The Goto Tech Guru is here to help!
By now, you've probably heard about the 75,000 Ransomware attacks that has hit 99 countries including the UK this past Friday, May 12, 2017. There are some reports of it hitting the USA as well. It is one of the broadest and most damaging cyberattacks in history.
For those not familiar with Ransomware, it is one of the most viperous forms on Malware that holds your computer hostage until you literally pay a ransom, usually $300-$500 USD. Even after you pay, it's often a scam and you never get they key to unlock your computer and it's files. What makes this particular attack so threatening, is that it did not require anyone to actually "click" on anything like an email attachment to affect them! Don't let this be you! In just the last year, Ransomware attacks have increased 50%, up from just 20% the prior year!!! It's a huge money maker for hackers, hence the growth. There are thousands of Ransomware's out there, some laying dormant on your computer until a specific date or action activates it! Things to help you prevent from being affected: 1) Keep up-to-date on all Windows patches 2) Keep all virus scan and malware scan software up-to-date 3) Don't open emails and attachments from even people you know if they look suspicious 4) Don't go to rogue or unknown websites. Even if you do the above, if you don't have the proper virus and malware scan software installed, you are quite likely still vulnerable. Due to this recent attack, for a limited time, I am offering a special: A quarterly checkup of your PC for just $225/year; less than $0.62 per day! This checkup includes a professional scan of your computer for virus/malware/ransomware PLUS an overall health check of your computer to determine other issues such as slowness and system aging issues. Enrolling in this offer will provide discounts to other services as well during your enrolled year! To make an appointment, contact: Manny The Goto Tech Guru [email protected] www.TheGoToTechGuru.com 240-670-GURU (business) 240-778-6730 (direct) Also visit us at: Twitter: @TheGoToTechGuru Facebook: @TheGoToTechGuru Most people don't know that Ransomware has been around since 1989. Did you know there are different types and variants?? Ransomware has gained great popularity in the hacking industry because why just infect a computer with a virus when you can hold it hostage and get good money??? Ransomware attacks rose from 3.8 million in 2015 to 638 million in 2016, an increase of 167 times year over year, according to Sonicwall — even as the number of malware attacks declined. Read here to learn the history of Ransomware and its future.
If there's an e-mail in your inbox asking you to open a Google Docs from someone, and you don't know who it is, don't open it. It's probably a phishing email disguised as a contact attempting to share a file from Google Docs, says Google. The email appears to come from someone inviting the user to share a document. The sophisticated email looks very similar to one sent by Google. For more information and details, see this article.
These are the 3 biggest ways Hackers steal your personal data off computers. The good news is you can stop them! Read this article and get smart on protecting yourself!
You've probably heard about people hacking into modern cars. Now Kaspersky Labs, a major developer of virus scan software, has test-hacked 7 cars to find their security vulnerabilities. In fact, they found it fairly easy. Although cars are not currently a major target, read this article for more.
We've likely all seen some sort of computer hacking on TV shows and movies. But how realistic are they? While it's often over dramatized (ie. it's much less exciting in real life), sometimes it's not that far off from the truth. The biggest difference is that in real life, it takes much longer than on TV. Surprised?? Read this article to see how it's done! Although often plausible, in many cases, fiction is truer than real life!
Your first reaction may be to change all your passwords, which is a great first step. But this is only the first of many steps in order to both protect yourself and eraticate any spyware, virus, malware or ransomware that may be making the situation with your PC even worse! Hopefully, you already have a full backup of your PC before the hack. But the first and best thing you can and should do, is disconnect it from the internet! If you need change passwords, do it from a different unaffected computer or tablet, even your smartphone. But by continuing to leave your PC connected to the internet, you are allowing the hacker to actively continue mining your affected PC for financial, medical, personal and other information! Worse, even with it disconnected from the internet but still powered on, any spyware or ransomware the hacker installed may continue to mine, propogate and thus spread! So your best bet is to turn your PC off and contact a professional to eraticate the problem. Of course there may be damage already done, such as possible loss of data and corruption to the operating system, but your goal is to minimize the damage so that your computer can be recovered to an operating status vs. having to reinstall the OS completely and lose everything. Here are some tips. For more information and to help you navigate this personal violation, contact TheGoToTechGuru!
Backing up your PC/Mac is the key to your sanity after a virus attack or hack. There's an old saying in Cyberspace: "The integrity of your data is only as good as your last backup!" There's nothing worse than to lose a year, 6 months or even a week's worth of work that you may not even be able to reconstruct! How about all those photos of your kids, anniversary or once-in-a-lifetime vacation? Fortunately, there are several options to back up your PC/Mac content online. It doesn't backup your operating system (eg. Windows or Mac OS), which you can more easily get, but these options will backup everything else if you so choose. Most of these services will automatically backup a file as soon as it's changed, such as a document, so you won't have to remember to do it manually. Of course, there's a nominal fee depending on the amount of backup storage you need, but it will be nothing compared to your sanity when you lose the precious photos and legal documents! Here is a review of several online backup services. For more information and to install these services, contact TheGoToTechGuru. If you prefer offline backups for more privacy, TheGoToTechGuru can provide a consultation on this option as well.
I recently had a customer that had his PC infected by Ransomware. For those of you not familiar with Ransomware, it’s a virus that encrypts all your files and holds them hostage until you pay the hostage taker $1000-$5000+. It’s well known that even if you do pay the exorbitant ransom, there’s still no guarantee that you’ll receive the key to unlock all your files. All his business and personal files were affected, including emails, which were all no longer accessible. To make things worse, he had no backup of anything.
To avoid getting virus’ and Ransomware, you must have good virus scan software AND malware prevention software. Don't depend on what comes with Windows because it's the minimum protection, which is only what my customer had. In the event a virus or malware does slip through, having a sound backups is the key to minimizing loss and letting you sleep at night. I strongly recommend the following virus and malware software: Kaspersky Internet Suite (most robust) and Malwarebytes Professional/Premium (industry leading software). For backups, I recommend Carbonite, which has unlimited storage for just $5.99/month and provides multiple versions of files you backup in case you accidently delete a file or make other changes you didn't mean to. Transmission and data storage is encrypted for security. Backed up data is available to your other computers, smartphone and tablets as well from free! For more information on Ransomware, Virus’, prevention software and backup software, contact TheGoToTechGuru. One of the biggest and more recent threats to your PC and it's data is Ransomware. It's a type of Malware that gets onto your computer via email, downloads, infected removable drives, infected software or websites. It locks all your data and software as well as your PC via it's operating system (e.g. Microsoft Windows) and holds it ransom until you pay someone literally thousands of $Dollars$ ... and even then, you may not get it all unlocked as there are many scams out there! Your only other alternative is to completely wipe your PC and reinstall everything from scratch instead of paying the ransom ... but even if you have a backup of your data, how current is it?? How many days/weeks/months or more of work would you lose in lost data? Do you have current backups of all your software? How many hours would it take you to reinstall Windows, your software and restore all it's data? How long would it take you to put back all the customizations you had? Here's a lot of what you need to know! For more information on how to protect yourself, call or email The GoTo Tech Guru!
It's a confusing world out there with Viruses & Malware! They're all bad, but what's the difference?? To understand and how they impact you, see the link below. Software protection against these will depend on how you use your PC/Mac. Remember, there's no 100% solution, but you can and should protect yourself! Read on here ...
|
Blog AuthorI love technology and how it enhances our lives! Just think, without the Apollo moon missions, we might not have calculators! Imagine!! Archives
October 2018
Categories
All
|






















 RSS Feed
RSS Feed