|
Security researchers have uncovered 89 malicious Google Chrome extensions on the official Chrome store that can inject ads, code to secretly mine cryptocurrency, and load a tool to record and replay a person's browsing activities. According to researchers at Trend Micro, this collection of extensions affected over 423,000 users and was used to form a new botnet called "Droidclub." Find out here which extensions these are and how they work. Learn more here about cryptocurrency, like Bitcoin.
#windows #mac #iphoneipad #android #security
0 Comments
There is a security bug in Skype's update process. It's so critical that if exploited, a hacker can take full control of your computer. Microsoft has said that it will not patch the issue since it will require a "large code revision." Although Microsoft engineers were able to replicate the exploit, they consider it a low-risk threat and the fix will be included in a "newer version of the product rather than a security update" instead.
Get the full scoop here and how you can protect yourself. #security #software There is a fairly new scam making the rounds. It's known as a porting or port-out scam. A fraudster finds out critical information about you such as your name, phone number, Social Security number, date of birth and more. Much of this information is obtainable on the Dark Web thanks to the massive Equifax data breach that we learned about last year.
A criminal that has your name, phone number, SSN, date of birth and more will call your mobile phone service provider pretending to be you, and tell them that you're switching to another company but want to keep your phone number. Transferring your number from say, Verizon to AT&T, is a process called porting. The porting process takes up to 24 hours to complete. During this time both phones will be functional. Meaning, any text messages that you receive on your phone will also be seen by the scammer on the phone your number is being transferred to. If you have two-factor authentication set up on your bank accounts, or any online sites for that matter, the scammer will be able to get the code needed to log into your account. From there, you could become a victim of identity theft and even have money stolen from your bank accounts. Now, don't let this turn you against two-factor authentication. It's an important security feature that you should be using whenever possible. The problem isn't two-factor, it's the criminals trying to rip you off. There are ways to prevent falling victim to these types of scams, keep reading for suggestions. #security #iphoneipad #android Microsoft has announced that Windows Defender, its built-in antivirus software for Windows 10, will start removing software that has “coercive messages” or “misleading content to pressure you into paying for additional services or performing superfluous actions.”
This type of software, commonly known as scareware, is typically found in cleaner apps that will supposedly optimize your registry on a Windows PC or promise to otherwise speed a machine up. “There has been an increase in free versions of programs that purport to scan computers for various errors, and then use alarming, coercive messages to scare customers into buying a premium version of the same program. See this article to understand more and what to do. #windows #security #news The latest attacks involving cryptocurrencies such as Bitcoin are outsmarting even the biggest tech companies around. Click on the wrong site and your computer could be hijacked by those looking to profit from cryptocurrency. While browsing online, you might suddenly hear your laptop’s fans whirring into life and your PC slowing to a crawl. A security scan might show no malicious files hiding in your PC. The problem goes away, and you move on. And yet, when you next come back to that same website, the problem starts again. The cause could be a type of malware that’s very hard to detect. In fact, when used legitimately, this software isn’t considered malware at all. Find out here what's going on! Learn more here about cryptocurrency, like Bitcoin,
#security #virus&malware When the CIA, FBI, and NSA all reach the same conclusion, you should probably listen. In the age of fake news, collusion, coercion, and bots, the heads of all three U.S. intelligence agencies agree on one thing: don’t buy Huawei phones. The intelligence community has been warning about the risk of Huawei for years, but the timing of the message here is clear: buy the Mate 10 Pro at your own risk. The intelligence community seemingly has ample reason to suspect Huawei of cyber espionage which has long been suspected of using its technology to spy on users. Huawei has been caught bribing users to leave glowing reviews for the new handset on BestBuy.com. Those comments have since been removed. Get the inside story here!
#security #news Recent news of the Meltdown & Spectre vulnerabilities in Intel’s processors has driven the wedge between the two even further, forcing Microsoft to do much of the work to patch security holes. This article provides insight into this every deepening rift.
#security #meltdown&spectre Apple is outsourcing its Chinese iCloud operations to a local firm in southern China starting on February 28th. The move has been known since last year when Apple announced its partnership with the firm. In February, Apple will transfer Chinese iCloud data to the GCBD-managed data center in Guizhou. It won’t make any visible difference to Chinese customers on the front-facing end, and Apple tells customers that data remains secure and private. “Apple has strong data privacy and security protections in place and no backdoors will be created into any of our systems,” it says. Get the details here and here.
#mac #iphoneipad #security Silicon Valley is making the bet that, in the near future, we’ll talk to all of our tech. But beware: the mechanism used to listen and turn what you say into a command for a virtual personal assistant or smart home gadget might not be secure. Security researchers have shown that they can generate an audio clip that sounds like innocuous speech, but actually gives a secret command to a voice transcription system, like the ones used by Amazon’s Alexa and Apple’s Siri. Find out here what happening under the hood and what you should be on the lookout for!
#security AMD is making firmware updates available for Ryzen and EPYC chip series owners and the company is planning to update older processors “over the coming weeks.” Like Intel, these firmware updates will be provided to PC makers, and it will be up to suppliers to ensure customers receive these. For details on how this may affect you, see this article.
#meltdown&spectre #security Microsoft has been forced to issue a second out-of-band security update this month, to deal with the issues around Intel’s Spectre firmware updates. Intel warned last week that its own security updates have been buggy, causing some systems to spontaneously reboot. Intel then buried a warning in its latest financial results that its buggy firmware updates could lead to “data loss or corruption.” Get the latest on this here.
#meltdown&spectre #security Intel Corp says that patches it released to address two high-profile security vulnerabilities, Meltdown and Spectre, in its chips are faulty, advising customers, computer makers and cloud providers to stop installing them. Get the latest scoop here!
#meltdown&spectre #security Mitigations for two critical architectural flaws in CPUs can cause performance degradation, but real-world impact is lower than synthetic benchmarks. Read here on how this will affect the cloud and you. As always, The GoTo Tech Guru is here to answer your questions and concerns. Just Contact Us!
#news #security According to Microsoft, if your PC over 2 years old, expect slowdowns from Spectre fixes, especially if you're not on Windows 10. The nature of the Spectre flaw means that fixes to guard against attacks also have the effect of slowing down computers in certain circumstances. Here's how the patches will affect you. To find out why and what to do, read here.
#news #security Microsoft has updated its support notice to say that Windows computers will not receive any security updates at all until their Anti-Virus (AV) software is certified compatible with the Spectre and Meltdown patches. Check here to see if your AV is on the list!
#news #security #windows Browser extensions are much more dangerous than most people realize. These small tools often have access to everything you do online, so they can capture your passwords, track your web browsing, log your keystrokes (and passwords), plus more. Popular browser extensions are often sold to shady companies or hijacked, and automatic updates can turn them into malware. It doesn’t mean that every extension is doing these things, but they can—and that should make you very, very wary. Here's how they work and how you can protect yourself!
#security People often don't think about their rights until they need them. Your data is the same -- you won't realize how important it is until you lose control of it. There is no such thing as perfect security. But no matter who you are or where you are in the world, there are a lot of things you can do -- many of which are simple -- to protect yourself! Here's a guide on how to secure your privacy in today's world. If you need help, just call The GoTo Tech Guru!
#security These days, unless you go to extraordinary lengths, nearly every piece of your personal and professional life goes through a cloud service. The risk of having important cloud credentials compromised is too great to rely on protecting them with nothing more than a password.
Two-factor authentication is no longer an optional feature. If you use modern cloud services, this extra layer of security can dramatically reduce the risk of a hostile takeover. Here's how to get started. As always, The GoTo Tech Guru is here to help with all your tech needs! #security Design flaws in processors from leading chipmakers could let attackers access sensitive information. The flaw impacts more than just Windows, Macs and iOS devices and affects most all computers, phones, tablets, watches, smart TVs and the like.
This is a flaw in the computer CPU chips at its most fundamental level and is NOT a virus, so cannot be eradicated by anti-virus or anti-malware software. It will require several levels of fixes to include no less than: the operating system, BIOs, and CPU driver. At this time, no hardware replacements are necessary, just firmware and software fixes. However, due to repair complexity, if not done properly and by a professional, it could render your device completely useless, otherwise known as "bricking". For questions or to have your computer repaired, call The GoTo Tech Guru! How did this happen and what's the fix? #security #news #iphoneipad #chromebook #mac #tv #virus&malware #windows #android Hardly a week goes by when you don't hear of yet-another-company admitting to a data breach, and the consequences of being compromised can be extreme. In 2016, Linux Mint to Swift, the Trump Towers to strings of hotel chains all lost customer account information, which paved the way for potential identity theft and fraudulent transactions.
Follow this simple checklist of best practices to protect your privacy and information without spending a cent! #security As of January this year, 2018, Google will start to mark websites without HTTPS as non-secure. Because of this, non-secure websites have had their ability to rank for searches on Google severely diminished.
Luckily for those affected by this change in Googles algorithm adding a standard SSL certificate to your site will allow visitors to securely connect to your website. An SSL certificate will secure all the pages on your website to provide you with: • A secure place for visitors to learn about and engage with your business • Increased visibility in search results! • Peace of mind that your business isn’t the next victim of a hacker For more information on SSL, read here. As always, The GoTo Tech Guru is here to help with this and all your IT needs. #security #news Apple’s revolutionary Face ID tech built-into its high-end iPhone X may very well be “years ahead” of competing facial recognition platforms — however that hasn’t stopped it from being spoofed! The latest Face ID “hack” proves that even our own flesh and blood can be a security liability. Find out here how this 10-year old spoofed his mother's iPhone X!
#iphone&ipad #security Facebook’s one-on-one encrypted messaging feature called Secret Conversations is now live for all Android and iOS users. Secret Conversations allows Messenger users to send end-to-end encrypted messages to their Facebook friends. After you send an encrypted message the person receiving it will have to agree to use the Secret Conversations feature. Once they do, they’ll see your message. Read here to find out how to use this wonderful feature. As always, The GoTo Tech Guru is here to help with your phone issues!
#iphone&ipad #android Police could soon have a device that could catch drivers red-handed. It's called a "textalyzer", modeled after a Breathalyzer. The police would see a screen that logs phone activity like the Facebook app, What's app, text messages and phone calls. Plus, everything has a time stamp. No actual content is revealed. The device can also tell the difference between a voice-activated text and typing. Read here for the full scoop.
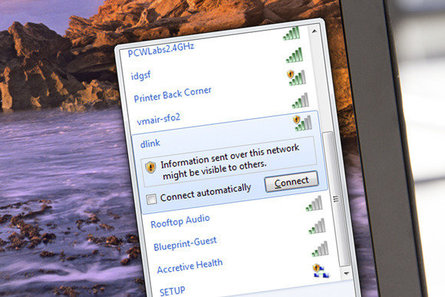
#security #news #iphone&ipad #android This is an older article but still just as illuminating! You’ve probably read at least one story with warnings about using unsecure public Wi-Fi hotspots, so you know that eavesdroppers can capture information traveling over those networks. But nothing gets the point across as effectively as seeing the snooping in action. Not only can a hacker see the website you're going to, they can hijack private accounts on popular Web services such as Gmail, LinkedIn, Yahoo, and Facebook.
Read this article on how it happens and how to protect yourself! As always, The GoTo Tech Guru is here to help you navigate these confusing waters! #security #wifi |
Blog AuthorI love technology and how it enhances our lives! Just think, without the Apollo moon missions, we might not have calculators! Imagine!! Archives
October 2018
Categories
All
|




















 RSS Feed
RSS Feed